May 3, 2026
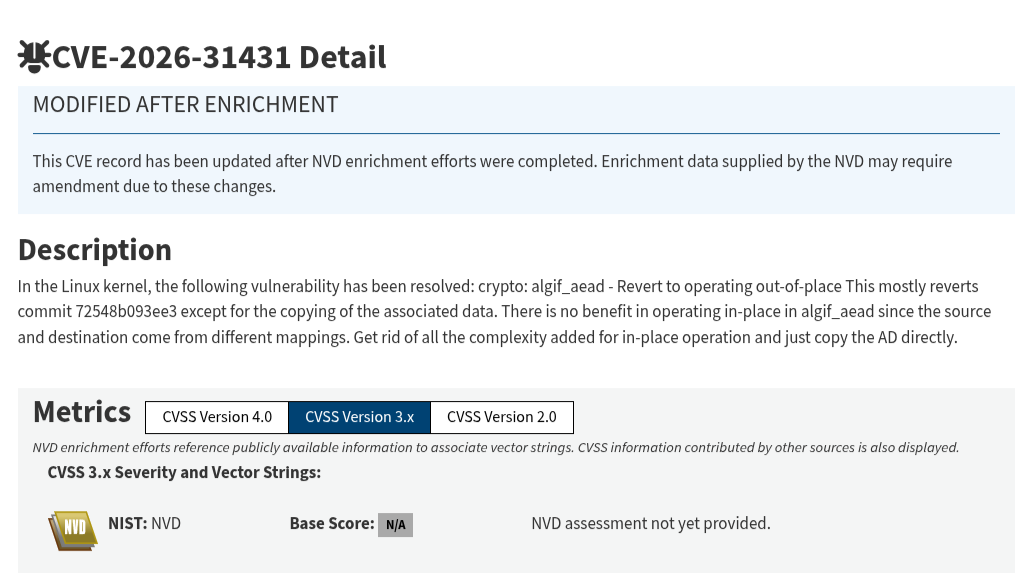
A new Linux kernel vulnerability CVE-2026-31431, better known as Copy Fail is a reminder of something backend engineers tend to underweight:
your application security model is only as strong as the system it runs on.
This isn’t a remote exploit. It’s a local privilege escalation (LPE). At first glance, that sounds less urgent until you remember how modern systems actually work:
- CI/CD pipelines
- Containers with shared kernels
- Third-party agents running on hosts
- Developers with partial access
All of those are footholds.
Copy Fail turns any of them into root access with high reliability. No race conditions. No fragile timing. No exotic setup.
That changes the threat model.
Why this matters for Ruby developers
If you’re building with Rails, chances are you’ve invested in:
- Strong authentication flows
- Authorization layers (Pundit, CanCanCan)
- Secure session handling
- Dependency auditing
All good. All necessary.
But none of that protects you if the underlying system lets an attacker rewrite privileged binaries in memory and escalate instantly.
This is the uncomfortable layer most app developers don’t own but absolutely depend on.
The real takeaway
This isn’t about kernel internals. It’s about responsibility boundaries.
As Ruby developers, we often assume:
“Infra will handle that.”
But in practice — especially in startups, small teams, or self-managed environments you are infra.
So the actionable shift is simple:
- Treat kernel updates as security patches, not maintenance
- Don’t rely on container isolation as a hard boundary
- Minimize local access wherever possible
- Know what’s running on your hosts not just your app
Opinion
Bugs like Copy Fail don’t just expose systems they expose assumptions.
And one of the most persistent ones in our ecosystem is this:
“If the Rails app is secure, the system is secure.”
It’s not.
Not even close.
